I know you’re in a hurry. Sysadmin’s time is so precious because we have to deal with the next incident or the next request or the next to-do.
So let’s get into it….
How to Set Up an Nginx Certbot
This is specific to nginx. BUT it is almost the same as if you are doing it for Apache. You just have to use it’s plugin.
What We Will Do. …
install Certbot, and then use it to get a free SSL certificate for Nginx on Ubuntu 18.04. We will also set up this certificate to renew automatically, so you don’t have to spend hours maintaining it. We will then test the system to make sure that everything is running smoothly.
The best practice for doing this is to use a separate Nginx server block file, rather than the default Nginx file.
In other words, virtualhosting
Prerequisites. …
efore starting this tutorial, you are going to need a few things. To my mind, the best solution to using your Ubuntu setup as a HTTPS server is to use a LEMP stack, and this is what I’m using in the following tutorial. I know that some people prefer a different setup, however, so I’ll list the absolute minimum requirements here:
- First, an Ubuntu 18.04 server set up and running. You will also need this server to have a sudo non-root user, and an operational firewall.
- A registered, working, and tested domain name. In this tutorial, I’m going to use example.com. There are plenty of ways to get a domain name cheaply, or even for free, or you can just use your existing registrar.
- For your domain name, you are going to need to have set up two DNS records. One should be an A record with example.com pointing to your server’s public IP, and the other another A record with example.com pointing to the same place.
- Once you have all this, go ahead and install Nginx on your server. This is pretty straightforward, but there are plenty of guides available if you get stuck. Make sure, when you install Nginx, that you also have a server block for your domain. In this tutorial, I will use /etc/nginx/sites-available/example.com as my example, but install the server block wherever is easiest for you.
Keep in mind that Nginx can also be used as a proxy server within your network environment. If you are using a proxy configuration, it complicates the SSL setup process but can still be done with Let’s Encrypt. To secure external traffic from end to end, you will need to actually obtain two separate SSL certificates.
Step 1: Install Certbot. …
$ sudo add-apt-repository ppa:certbot/certbot
$ sudo apt update
$ sudo apt install python-certbot-nginxStep 2: Configure and Confirm Nginx. …
$ sudo nano /etc/nginx/sites-available/example.com
With the file open, look or search for the server_name line. It should look like this:
…
server_name example.com www.example.com;
…
If it does, good.
If it doesn’t, you are going to have to tell Nginx where to look. To do so, update the line to point it to the right domain. Then save and close the document. This should be all you have to do, but it is worth checking at this point that everything is well. You can check that your edits make sense to Nginx by running it from the command line:
$ sudo nginx -t
If you get an error, something went wrong. The most likely source is a typo in your own edits, so go back and check the file for those. Once you’ve got this command running with no errors, you can move on.
The next step is to re-start Nginx so it will use the correct server block. To do this, you will need to make a system call, but don’t worry. Run this command:
$ sudo systemctl reload nginx
At this point, Nginx should report that it found the correct server block.
So far so good.
Step 3: Allow HTTPS Traffic Through your Firewall. …
$ sudo ufw status
The output should look something like this:
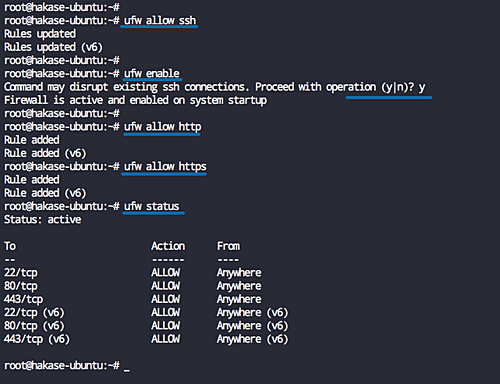
As you can see, at the moment only HTTP traffic is allowed through your server, so you need to tell ufw to allow HTTPS through. Nginx already comes with a profile that will allow this, so all you need to do is enable it:
$ sudo ufw allow 'Nginx Full'
Then disable the obsolete Nginx HTTP profile by deleting it:
$ sudo ufw delete allow 'Nginx HTTP'
To check that these commands worked, you can verify the configuration settings for ufw in the same way as before. Run the same status command:
$ sudo ufw status
And you should see that the output has changed, so now HTTPs is permitted:
Status: active To Action From -- ------ ---- OpenSSH ALLOW Anywhere Nginx Full ALLOW Anywhere OpenSSH (v6) ALLOW Anywhere (v6) Nginx Full (v6) ALLOW Anywhere (v6)
So you should now have Nginx installed, with a ufw set up that will allow HTTPs traffic through.
Step 4: Get an SSL Certificate. …
$ sudo certbot --nginx -d example.com -d www.example.com
Step 5: Verifying Auto-Renewal for Certbot. …
$ sudo certbot renew --dry-run